Web Security: Protecting Your Site from Threats
Discover the importance of web security and learn how to protect your website from various online threats. We'll dive into tools, practices, and strategies that bolster your site's defenses.

The Importance of Web Security
Web security is no longer a luxury — it is an essential requirement for every online business. With the enormous growth of e-commerce, online banking, and social networking, the internet has become a primary target for cybercriminals seeking to exploit vulnerabilities for malicious intent. A lack of proper web security could lead to severe consequences, including:
- Data breaches: Unauthorized access to sensitive information like financial details, personal records, or intellectual property can lead to financial loss, reputation damage, and even legal penalties for businesses.
- Loss of user trust: Security incidents can undermine user confidence, driving them to competitors' sites or avoiding your services altogether.
- Website downtime: Cyberattacks can disrupt operations and render websites inaccessible, causing customer dissatisfaction and potential lost revenue.
- Legal consequences: Organizations handling sensitive user data may face legal action if they fail to implement adequate security measures or adhere to data protection regulations such as GDPR or CCPA.
- Reputation damage: A security breach can tarnish a company's image, creating long-term consequences that may be challenging to recover from.
In short, web security is vital for protecting sensitive data, safeguarding user privacy, maintaining a website's reputation, and ensuring business continuity. A secure website instills trust in visitors, enabling the growth and success of online businesses.
Common Web Security Threats
There are numerous cyber threats that websites face daily. Understanding these threats is the first step towards securing your online presence. Here are five common web security threats:
- SQL Injection: This occurs when an attacker injects malicious SQL code into input fields or URLs to manipulate database queries and gain unauthorized access to sensitive information. SQL injection can lead to data theft, unauthorized access, or even complete control over a website's backend.
- Cross-Site Scripting (XSS): In an XSS attack, malicious scripts are embedded into web pages, which then execute in the user's browser. These attacks can lead to stolen user credentials, personal information, or altered site content.
- Cross-Site Request Forgery (CSRF): In a CSRF attack, an attacker tricks a user into executing unwanted actions on a website in which they are authenticated. This could involve actions such as transferring funds, changing passwords or email addresses, or making unauthorized purchases.
- Distributed Denial of Service (DDoS): DDoS attacks involve overwhelming web services with excessive traffic, rendering them inaccessible to legitimate users. This can cause significant disruption to business operations, resulting in lost revenue and customer dissatisfaction.
- Malware infections: Cybercriminals may exploit vulnerabilities in a website's code to plant malware, which can then be used to steal sensitive data, launch other attacks, or even take full control of the affected site.
To counter these threats, businesses must implement a variety of web security measures and strategies tailored to their specific needs and risk profiles.
Securing Your Web Application
A secure web application is the backbone of online business operations. Implementing various security measures can substantially reduce the likelihood of cyberattacks and protect your website from potential threats. Here are some essential steps for securing your web application:
- Use HTTPS: HTTPS encrypts traffic between a user's browser and your website, ensuring data confidentiality and integrity. Obtain an SSL certificate and ensure your website is configured to use HTTPS by default.
- Proper input validation and output encoding: Validate all user inputs to prevent malicious data from being processed, and use output encoding to mitigate the risk of XSS attacks by escaping special characters that might be interpreted as malicious code.
- Secure password storage: Properly store user passwords using strong, adaptive hashing algorithms like bcrypt, scrypt, or Argon2, coupled with a unique salt for each password. This makes it significantly more difficult for attackers to crack stolen password hashes.
- Implement access controls: Ensure that users only have access to the resources and actions pertinent to their role. Use the principle of least privilege, granting users the minimum permissions necessary to fulfill their tasks.
- Adopt a secure Software Development Life Cycle (SDLC): Integrate security into every stage of the application development process: planning, design, implementation, testing, and maintenance. This helps in detecting and addressing vulnerabilities early, reducing the risk of security incidents.

By following these principles, you can lay the foundation for a secure web application that withstands the ever-evolving threats.
Best Practices for Strengthening Your Site's Defense
Implementing strong security measures in your web applications can protect your site against a myriad of threats. Here are some best practices for building a more strong defense for your site:
Keep Your Software and Plugins Updated
Always install timely updates for your web application's software, plugins, and any third-party dependencies. Updates often include security patches to fix vulnerabilities that can be exploited by attackers. Enable automatic updates whenever possible to ensure your software is always up to date and protected.
Secure Server and Database Configuration
Ensure proper server and database configurations to minimize the risk of unauthorized access. This includes disabling unnecessary services, configuring strong passwords, controlling remote access, and setting up firewalls. Regularly review and audit security configurations to identify potential weaknesses and address them.
Implement SSL/TLS Certificates
Employ SSL (Secure Sockets Layer) or TLS (Transport Layer Security) certificates to encrypt data transfers between your server and users' browsers, protecting sensitive information such as user credentials and payment details. Display the secure HTTPS address and padlock icon in the user's browser to instill trust and improve overall security.
Enforce Strong Authentication and Authorization Measures
Implement authentication and authorization methods to ensure only authorized users have access to sensitive resources. Incorporate multi-factor authentication (MFA), strong password policies, account lockout mechanisms, and session timeout features to minimize security risks.
Validate User Input and Output-Encoding
Input validation and output encoding can prevent common vulnerabilities such as SQL injection, cross-site scripting (XSS), and remote code execution. Check and sanitize all user inputs, including form fields, URL parameters, and cookies. Additionally, properly encode data when displaying it to users to avoid potential attacks.
Regularly Conduct Security Audits and Vulnerability Assessments
Perform security audits and vulnerability assessments on your web application to identify potential weaknesses and verify compliance with security best practices. Use automated tools and manual testing to detect and fix vulnerabilities before they can be exploited by cybercriminals.
Foster a Culture of Security Awareness
Educate your team on the importance of web security and provide them with the necessary training, resources, and guidelines. Encourage a proactive approach where everyone plays a role in maintaining the security of the web application.
Choosing the Right Web Security Solutions
Selecting web security solutions that align with your specific requirements is crucial. When evaluating solutions, consider the following factors:
Ease of Integration
Choose a solution that integrates easily with your existing infrastructure and technology stack. Seamless integration will minimize disruptions and ensure quick deployment.
Scalability
A scalable solution enables you to accommodate an increasing number of users and handle growing amounts of data without compromising security. Look for a solution that can grow with your web application's needs to ensure seamless security management.
Performance Impact
Select a solution that maintains strong security while minimizing the impact on your web application's performance. Speed is essential for delivering a positive user experience, so ensure that your chosen solution does not adversely affect site load times or responsiveness.
Vendor Reputation
Choose a solution from a reputable vendor to ensure that you receive timely updates, support, and access to new features. Read reviews, compare testimonials, and research the vendor's history to make an informed decision.
Cost
Consider both the initial investment and ongoing expenses when selecting a solution. Assess whether the features offered align with your budget and business goals while still providing value-added security.
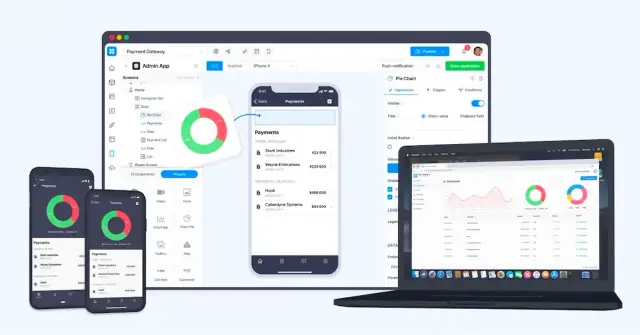
When evaluating your options, consider the benefits of AppMaster.io, a powerful no-code platform that simplifies application development and ensures security by regenerating applications from scratch when requirements change.
Monitoring and Response: Staying Ahead of Threats
Proactive monitoring and quick response measures can help you stay ahead of emerging threats and minimize potential damage. Implement the following strategies to stay informed and respond effectively:
- Set Up Automated Monitoring Tools: Employ automated solutions to detect and alert on security events. These tools can help you identify unusual activity, potential threats, and breaches in real-time, enabling you to respond quickly and minimize damage.
- Develop Incident Response Plans: Prepare and maintain an incident response plan that outlines the steps your team should take in the event of a security breach or cyberattack. Train your team on the plan and conduct regular drills to ensure the effectiveness of the response strategy.
- Continuously Enhance Your Security Posture: Stay up-to-date with the latest security trends and best practices to continuously improve your web application's defenses. Regularly review security configurations, update policies, and apply patches as needed.
- Learn from Security Incidents: Analyze any security incidents that occur and use the lessons learned to improve your web application's security. Update your incident response plan based on the findings and share the insights with your team to strengthen prevention and response capabilities.
Securing your website from threats is an ongoing process that requires constant vigilance and adaptation. Implementing best practices, choosing powerful security solutions, and fostering a culture of security awareness are essential to ensuring the continued success of your online presence. By leveraging the power of AppMaster.io's no-code platform and focusing on web security, you can keep your site safe and protected, instilling confidence in your users and aiding in your site's long-term growth and success.
How AppMaster.io Contributes to Enhanced Web Security
Optimizing web security is crucial for any online venture, and using the right tools can significantly impact your site's defenses. AppMaster.io is a powerful no-code platform focused on simplifying application development while rigorously maintaining security.
In this section, we'll explore how AppMaster.io enhances web security by eliminating technical debt, regenerating applications from scratch, and offering secure infrastructure and architecture.
Eliminating Technical Debt through Regeneration
One of the central tenets of AppMaster.io is the elimination of technical debt. Whenever requirements change, it regenerates applications from scratch. This approach ensures that your web applications don't accumulate outdated code, vulnerabilities, or inconsistencies that cybercriminals can exploit. As a result, you get a clean, secure, and efficient application while saving the time and effort required for constant monitoring and patching.
Secure Infrastructure and Architecture
AppMaster.io provides a secure infrastructure designed to sustain the complete application lifecycle. It uses the Go language (Golang) for server-side applications, Vue3 framework and JS/TS for web applications, and Kotlin and Jetpack Compose for Android or SwiftUI for IOS in mobile applications. These technologies have a strong focus on performance and security, which translates into reliable applications that can withstand various attack vectors.
Moreover, AppMaster.io applications support Postgresql-compatible databases, ensuring compatibility and security with a dependable database technology. The resulting applications boast solid scalability, making them suitable for high-load and enterprise use cases.
Comprehensive Security Measures and Best Practices
AppMaster.io integrates security best practices throughout the development process, promoting secure coding standards, API development, and application hosting. While creating backend, web, and mobile applications, the platform enables developers to implement security measures such as proper input validation, output encoding, and secure password storage. By automating many security tasks, it allows developers to focus on features and enhancements, knowing that their applications' security is taken care of.
Adapting to Emerging Security Threats
The sphere of web security threats is ever-evolving, and the AppMaster.io platform is designed to adapt swiftly to these changes. By regularly monitoring emerging threats and adjusting development practices and technologies, AppMaster.io ensures that your web applications' security remains current and capable of withstanding new vulnerabilities. This adaptability, combined with the elimination of technical debt, helps businesses continue to offer secure and trustworthy applications to their users.
In conclusion, web security is a critical facet of online business success, and using the right tools and strategies can mitigate risks and protect your site from various online threats. AppMaster.io offers a comprehensive solution for web security through technical debt elimination, secure infrastructure and architecture, and adherence to security best practices. With AppMaster.io, you can develop and maintain secure web applications that instill trust in your visitors and support your business's growth.
FAQ
Web security is essential to protect sensitive data, safeguard user privacy, maintain a site's reputation, and ensure business continuity. A secure website instills trust in visitors, enabling the growth and success of online businesses.
Common web security threats include SQL injection, cross-site scripting (XSS), cross-site request forgery (CSRF), distributed denial of service (DDoS) attacks, and malware infections.
Securing your web application involves implementing various measures such as HTTPS, proper input validation, output encoding, secure password storage, access controls, and adhering to security best practices throughout the application development process.
Best practices include updating software and plugins, securing server and database configuration, implementing SSL certificates, enforcing strong authentication and authorization measures, conducting regular security audits, and raising security awareness among your team.
Select a web security solution that meets your specific needs by assessing factors such as ease of integration, scalability, performance impact, compatibility with your tech stack, and cost. Read reviews, compare features, and consider free trials to make an informed decision.
Monitoring helps you identify unusual activity and potential threats, while timely response ensures you can mitigate risks before they cause irreparable damage. Use a combination of automated monitoring tools and manual procedures to stay alert and proactive in addressing security vulnerabilities.
AppMaster.io is a powerful no-code platform that simplifies the application development process while ensuring security by regenerating applications from scratch whenever requirements change. This eliminates technical debt and reinforces the security of your web applications.
Yes, numerous resources are available to help you stay up-to-date with web security practices, including blogs, podcasts, webinars, conferences, and online courses. Additionally, keep track of security alerts and updates issued by software vendors.





