What is user authorization?
Learn how to check if the user is authorized in the AppMaster
The term authorization often comes up when application security is discussed. You need to know exactly who is using your product and how. Otherwise, attackers can access important information. Therefore, sometimes it becomes necessary to check whether the user is authorized in the application and what he has access to. Learn how to do it and review the authorization concept in this article.
What is user authorization?
Often the concept of authorization is confused with user authentication. What is authorization? Authorization is the process of checking whether a user has the right to perform specific actions. On the other hand, authentication is responsible for verifying the user's identifier. Logs and a password most often act as an identifier. For example, how it works in an electronic store: the authentication process is performed at the moment when the user logs into his personal account. A check is made that such a user exists at this time. Authorization is launched only when the user starts to perform some action in the store, for example, adding a product to the cart. Simply said, authentication answers the question "who are you?" when authorization helps to understand "what can you do?" and determine what data, actions, and application features you have access to. The authorization process is much more complicated. It also includes the concepts of user groups, roles and their hierarchy, and types of actions.
Authorization types
There are several types of authorization.
Role-based authorization. In this case, the administrator assigns one or more roles to the user, which provide him with access to specific parts and functions of the application, various pages, and components. This approach helps define a hierarchy in organizations. For example, when access to certain data changes depending on the position: a user with the editor role has access to all publications and the right to edit them, while the author can only change his own publications and can read publications of other authors.
Discretionary access control (DAC). With this approach, access rights are granted to a specific user or group of users. The subject, the owner of the object, sets the rights to it for each individual user. A simple example of a selective model is Google Docs, where the owner can transfer and limit access rights to other users.
Mandatory authorization model. In this model, a confidentiality level is assigned to each element in the system. Users are given an access level that determines which objects they can interact with. This model is usually used in systems where there are increased security requirements.
Authorization in AppMaster
In applications that you create in AppMaster, user registration is represented by the Auth module. It allows you to create and edit user groups and access rights to them. When you create a project, the module is already built into it.
Module settings allow you to manage the following actions:
-
enable the registration in the application;
-
create a list of user groups with registration access;
-
set up user sessions;
-
create and edit groups of users.
How to check if the user is authorized in the application?
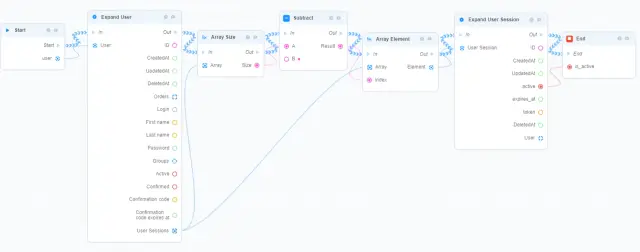
Authorization checking is most often related to security and is needed to ensure that the user is authorized and has access rights to certain parts of the application. In AppMaster, to check if the user is authorized in the application, you need to create a business process. We pass the USER object to the business process and get a list of its sessions. The last session in the array is the last active user session in the application. In response to the business process, we return Active. If Active is true, then the user is authorized.
That is how you can quickly check the user's authorization in an application created in AppMaster.





